Video is increasingly at the nexus of opportunity and danger for human rights activists. Video helps activists to document, confront, circumvent, and lobby against oppressive authorities—but it also allows those authorities to stalk them. Here's what we think will happen in 2013.
Both those using video for good and for evil made big advances in 2012. Activists marshaled video in new ways to tell their stories, share their evidence, and form their communities online. Activists in Brazil told the story of forced evictions [1] ahead of the World Cup. Activists documented military attacks on civilians in Syria [2]. Activists in Burma documented large-scale attacks [3] on the Rohingya minority.
Activists used video to tell their stories—and they succeeded in raising awareness of issues that risked being lost in the cacophony of world affairs. In return, repressive governments developed new ways to use video to target activists.
2013 will undoubtedly see the next stages of this video tech race—in fact, they’ve already taken shape. Activists and their allies are developing defensive security innovations, and we’ll soon see these tools protecting activists as they use video to advance their causes.
Top Video Security Threats of 2012
1. Video as Lure for Malware
‘Important new video’ popped up in many Syrian Skype chats in the spring and summer of 2012. The intriguing but unremarkable message seemed to contain an innocuous pdf file, but it also came with spyware called “Blackshades.” Using video as a lure, allies of the Syrian regime could now spy through the camera’s webcam, access any file they wanted, and watch every key that was pressed–including passwords. They could use what they learned to target the activist, or to infiltrate his network. The software developer has since suspended new sales, and BlackShades can now be found and removed [4]. But in many cases, the damage was done. Similar attacks in 2012 were waged against Uyghur [5] activists in China, and others in Bahrain [6], and a fake version of YouTube [7] was created to target Syrian activists.

Video activist Abdel Karim al-Oqda, aka Abu Hassan, was killed by Syrian government forces in 2012
2. Identification through Video
Using online videos to identify and target individuals was not a new trend—but regimes rolled it out on a larger scale [8] in 2012, with increased effectiveness and heightened consequences. Video activists often lack the capacity and resources to effectively protect their own identity, as well as the identities of individuals in the videos they’re filming. In 2012, individuals on both sides of the camera were identified and targeted. A prominent videographer [9] was killed; another activist was arrested [10] merely for having the live-streaming app Bambuser [11] on his phone. As video becomes an increasingly central battlefield, anonymity can literally be a life-or-death issue.
3. Evidentiary Failings of Video
One of the biggest threats to activist video is one you might not think of. Activists worldwide are risking their lives to record video that documents atrocities. Both judicial and journalistic bodies may be unable to use videos [12] if they can’t adequately establish the location, the date, and the civilian status of victims, among other things. Much of it lacks the supporting evidence to stand up in court—say, at the International Criminal Court [13] or your newspaper of choice [12]—and the risks these filmmakers take can be in vain.
Top Video Security Solutions for 2013
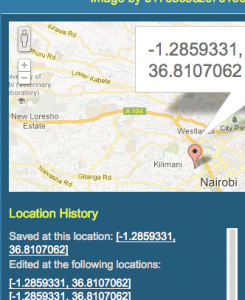
1. InformaCam
Video activists who want their video to have the credibility to stand up in a court room or a news room can follow a set of guidelines [14]. Soon, those using Android cell phones can use InformaCam [15]. This app automatically embeds data into the video file, such as location (from GPS sensors and wifi signals), and time (from internal clocks). It also creates a ‘digital fingerprint’ to tie a video to a specific camera. Because all of this can be used against activists by the repressive forces they’re fighting, everything is encrypted to keep it safe. WITNESS and our partners at the Guardian Project are developing InformaCam, and we recently received a Knight News Challenge grant [16] to help support the project.
2. Anonymity via ObscuraCam & the YouTube Blurring Tool
 YouTube’s facial blurring tool [17] automatically detects faces in videos, and blurs them to protect the individuals’ identities. This is a huge development—activists use YouTube far more than any other platform to share their video, and this has the potential to save lives. It doesn’t protect video before it’s uploaded, though, which is one reason that WITNESS and the Guardian Project are developing ObscuraCam [18]. ObscuraCam also removes all identifying data stored in photos, including GPS location, data, and phone make and model. These tools can protect individuals who may not even know they’re being filmed, let alone have given their consent.
YouTube’s facial blurring tool [17] automatically detects faces in videos, and blurs them to protect the individuals’ identities. This is a huge development—activists use YouTube far more than any other platform to share their video, and this has the potential to save lives. It doesn’t protect video before it’s uploaded, though, which is one reason that WITNESS and the Guardian Project are developing ObscuraCam [18]. ObscuraCam also removes all identifying data stored in photos, including GPS location, data, and phone make and model. These tools can protect individuals who may not even know they’re being filmed, let alone have given their consent.
3. Platform Alternatives
Although some platforms are making efforts to protect the activists who use them, like YouTube with its face-blurring tool, there are still many vulnerabilities that can be exploited with tragic consequences. Skype, a popular tool for video chatting and also sending videos from one activist to another, has recently come under fire. So why not try an alternative? In an impressively thorough article [19], Lifehacker suggests Jitsi [20] as a safer alternative to Skype. Jitsi encrypts both ends of the conversation, stores nothing online, and uses more secure protocols so “you don't need to worry about that data falling into the wrong hands.” The article also suggests safer alternatives to Facebook (Glassboard [21]) and Dropbox (SpiderOak [22]).
For Better and for Worse: The Revolution Will be Televised
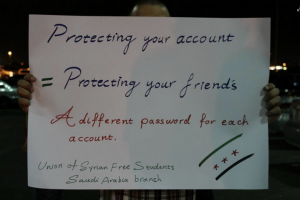
A photo shared by the Saudi Arabia Branch [23] of the Union of Syrian Free Students.
“Protecting Your Account = Protecting Your Friends
A different password for each account”
Videos spread through trusted networks that, like so many things involving human rights video, are a double-edged sword. The Saudi Arabia branch of the Union of Syrian Free Students [24] shared this message because activists’ digital security is increasingly fragile and increasingly important. Video images, social networks, and threats of violence are colliding in very powerful, very dangerous ways.
Wherever human rights issues are being fought, both sides will seek to use video technology. WITNESS will be following these issues through 2013 and beyond.
